Below is the handout from a talk I gave today at my internship with the World Organization for Human Rights USA, which focuses on impact litigation. Attorneys face special risks to their computer security because they are regularly in possession of confidential documents.
Assumptions:
- You already have a working, updated anti-virus system on your laptop;
- You know not to open attachments from strangers (and you do not let your email program do so either);
- You do not let strangers have unsupervised physical access to your laptop.
3 Technical Tips:
- Get to know your computer’s rhythms: if she slows down suddenly, or starts having weird pop-ups, run anti-virus immediately.
- Know the security holes of your operating system. Windows is famously insecure, and many anti-piracy technologies make it even less secure. OSX is more secure, but not perfect.
- Use https for your email (its a setting in Gmail)
- It is what all online banking and sales websites use—good enough for most people’s email needs
- “According to security expert Gene Spafford, [using https] is analagous to ‘using an armored truck to transport rolls of pennies between someone on a park bench and someone doing business from a cardboard box’” (What is https). More on behavioral security next.
A cartoon from xkcd on technical vs behavioral security:
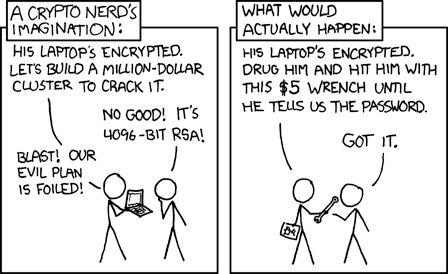
3 Behavioral Tips:
- Your laptop security is only as good as your personal security
- Even if a laptop is impenetrable remotely (which is nearly impossible), if it can be stolen it can probably be hacked
- Change or rotate passwords about every 6 months, and make them memorable enough that you do not have to write them down. Secure password trick: use a line from a favorite poem that has punctuation*
- Treat your laptop like cash: do not flash it in public and do not leave it unattended
3 Tips on How to Learn How Hackers Think
- Cryptonomicon by Neal Stephenson
- It is a fictional work about the history of cryptography, starting in WWII and ending up in the late 1990s. Reading it is a great way to learn how cryptographers think about security.
- Black Hat and DefCon
- These are the two largest information security (ie, hacker) conferences. They are both in Las Vegas in the fall. Defcon’s forums are worth reading. (Black Hat also has Washington DC training sessions).
- The Broken is a web-series on hacking. In the first episode, learn how to hack into WiFi networks (actually doing this may not be legal, but learning how it can be done is education).
Final Tip:
Think of your laptop like a house—your locks have to fit your needs. If someone is really determined, he will be able to get into your house, no matter your security system. This does not mean you cannot leave valuables in your house. It means understand that there is always a risk that something will be stolen, and the best anyone can do is mitigate that risk.
*You can think outside the box with passwords. All of the following were rated Very Strong by PasswordMeter.com:
- Twas in the Merry Month of May /
- “Impossible! for a plain…
- Who am I?24601!
- 1/4 tbs milk?
- ATCA (1789)
NOTE: don’t use these, since they are here. Choose a song or poem that is personally meaningful to you!
Inspirational Quote:
Amelia Earhart – “The most effective way to do it, is to do it.”
of course, now that you’ve said them, remind everyone they shouldn’t use those exact passwords 😉
Totally.